
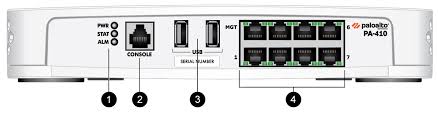
PA-410
The world’s first ML-Powered NGFW enables you to prevent unknown threats, see and secure everything— including the internet of things (IoT)—and reduce errors with automatic policy recommendations.
Description
Highlights
- World’s first ML-Powered NGFW
- Eleven-time Leader in the Gartner Magic Quadrant for Network Firewalls
- Leader in the Forrester Wave: Enterprise Firewalls, Q1 2024
- Spans a range of performance needs for the distributed enterprise with a broad lineup
- Offers security in a desktop form factor
- Supports high availability with active/active and active/passive modes
- Delivers predictable performance with security services
- Features silent, fanless design with optional redundant power supply for branch and home offices
- Simplifies the deployment of large numbers of firewalls with optional Zero Touch Provisioning (ZTP)
- Supports centralized administration with Panorama® network security management
- Maximizes security investments and prevents business disruptions with Strata™ Cloud Manager
Key Security and Connectivity Features
ML-Powered Next-Generation Firewall
- Embeds machine learning (ML) in the core of the firewall to provide inline signatureless attack prevention for file-based attacks while identifying and immediately stopping never-before-seen phishing attempts.
- Leverages cloud-based ML processes to push zero-delay signatures and instructions back to the NGFW.
- Uses behavioral analysis to detect internet of things (IoT) devices and make policy recommendations; is a cloud-delivered and natively integrated service on the NGFW.
- Automates policy recommendations that save time and reduce the chance of human error.
Identifies and Categorizes All Applications, on All Ports, All the Time, with Full Layer 7 Inspection
- Identifies the applications traversing your network irrespective of port, protocol, evasive techniques, or encryption (SSL/TLS). In addition, it automatically discovers and controls new applications to keep pace with the SaaS explosion with SaaS Security subscription.
- Uses the application, not the port, as the basis for all your safe enablement policy decisions: allow, deny, schedule, inspect, and apply traffic shaping.
- Offers the ability to create custom App-ID™ tags for proprietary applications or request App-ID development for new applications from Palo Alto Networks.
- Identifies all payload data within the application (e.g., files and data patterns) to block malicious files and thwart data exfiltration attempts.
- Creates standard and customized application usage reports, including software-as-a-service (SaaS) reports that provide insight into all sanctioned and unsanctioned SaaS traffic on your network.
- Enables safe migration of legacy Layer 4 rule sets to rules based on App-ID with Policy Optimizer built in, giving you a rule set that is more secure and easier to manage.
Enforces Security for User Devices Anywhere While Adapting Policies Based on User Activity
- Enables visibility, security policies, reporting, and forensics based on users and groups—not just IP addresses.
- Easily integrates with a wide range of repositories to leverage user information: wireless LAN controllers, VPNs, directory servers, SIEMs, proxies, and more.
- Allows you to define Dynamic User Groups (DUGs) on the firewall to take time-bound security actions without waiting for changes to be applied to user directories.
- Applies consistent policies irrespective of users’ locations (office, home, travel, etc.) and devices (iOS and Android mobile devices; macOS, Windows, and Linux desktops and laptops; Citrix and Microsoft VDI; and terminal servers).
Prevents Malicious Activity Concealed in Encrypted Traffic
- Inspects and applies policy to SSL/TLS-encrypted traffic, both inbound and outbound, including for traffic that uses TLSv1.3 and HTTP/2.
- Offers rich visibility into TLS traffic, such as the amount of encrypted traffic, SSL/TLS versions, cipher suites, and more, without decrypting.
- Enables control over use of legacy TLS protocols, insecure ciphers, and misconfigured certificates to mitigate risks.
- Facilitates easy deployment of decryption and lets you use built-in logs to troubleshoot issues, such as applications with pinned certificates.
- Lets you enable or disable decryption flexibly—based on, for example, URL category, source and destination zone, address, user, user group, device, and port—for privacy and regulatory compliance purposes.
- Allows you to create a copy of decrypted traffic from the firewall (i.e., decryption mirroring) and send it to traffic collection tools for forensics, historical purposes, or data loss prevention (DLP).
- Allows you to intelligently forward all traffic (decrypted TLS, undecrypted TLS, and non-TLS) to third-party security tools with a network packet broker and optimize your network performance and reduce operating expenses.
Best-in-Class Cloud-Delivered Security Services Powered by Precision AI
- The typical enterprise’s attack surface has grown significantly with the mass adoption of hybrid work, cloud, IoT, and SaaS. Furthermore, the threat landscape is rapidly intensifying due to the ability to easily access and use hacker-friendly tools and resources in their campaigns. Traditional network security solutions and approaches are no longer effective. With Palo Alto Networks Cloud-Delivered Security Services, customers can benefit from best-in-class, real-time security to help them protect all users, devices, and data in their network, regardless of location.
- Palo Alto Networks security services use the power of Precision AI® inline to stay ahead of threat actors and stop new and never-before-seen threats in real time. Through shared threat intelligence across over 70,000 customers worldwide, they have insights into emerging threats and can act proactively. Finally, seamless integration with NGFW and SASE eliminates security gaps and offers customers a single pane of glass to view and manage their security.
Services include:
- Advanced Threat Prevention: Stop known and unknown exploits, malware, spyware, and command-and-control (C2) threats, including 60% more injection attacks and 48% more highly evasive C2 traffic than traditional IPS solutions with industry-first zero-day attack prevention.
- Advanced WildFire: Ensure safe access to files with the industry’s largest malware prevention engine, stopping up to 22% more unknown malware and turning detection into prevention 180X faster than competitors.
- Advanced URL Filtering: Ensure safe access to the web and prevent 40% more threats in real time than traditional filtering databases with industry-first prevention of known and unknown phishing attacks, stopping up to 88% of malicious URLs at least 48 hours before competitors.
- Advanced DNS Security: Protect your DNS traffic and stop advanced DNS-layer threats, including DNS hijacking, all in real time with 2X more DNS-layer threat coverage than competitors.
- Next-Generation CASB: Discover and control all SaaS consumption in your network with visibility into 60,000+ SaaS apps and protect your data with 28+ API integrations.
- IoT Security: Secure your blind spots and protect every connected device unique to your vertical with the industry’s most comprehensive Zero Trust solution for IoT devices, discovering 90% of devices within 48 hours
Enables SD-WAN Functionality
- Allows you to easily adopt SD-WAN by simply enabling it on your existing firewalls.
- Enables you to safely implement SD-WAN, which is natively integrated with our industry-leading security.
- Delivers an exceptional end-user experience by minimizing latency, jitter, and packet loss.
Firewall throughputrn(appmix): 1.4 Gbps
Threat Preventionrnthroughput (appmix): 0.8 Gbps
IPsec VPNrnthroughput: 0.65 Gbps
Max concurrentrnsessions : 64,000
New sessions perrnsecond : 11,000
Virtual systemsrn(base/max): 1/1
